Implementing robust threat detection and prevention strategies has become as important as maintaining operational continuity for businesses. In other terms, strong threat detection tactics ensure disruption-free business operations. However, businesses often fail to adopt a holistic approach that not only detects but also eliminates threats.
Artificial intelligence in cybersecurity can play the role of a catalyst while ensuring resilient threat detection and prevention. AI-driven threat detection can offer 24/7 coverage, enabling automated and real-time alerts for incidents. In 2026, implementing AI in cybersecurity has become a common practice, with 90% organizations having an active strategy or preparing to have one.
Nevertheless, it is crucial to adopt AI responsibly for cybersecurity, considering the prevailing risks and limitations. This blog will discuss AI-enabled cyber threat detections, their benefits, use cases, and limitations so that you can adopt AI effectively. Let’s get started...
What is AI-Driven Threat Detection?
AI-driven threat detection is a strategy in which businesses and security teams integrate AI technologies to identify cyber threats. Such an approach offers an automated process to detect and mitigate cybersecurity threats, protecting endpoints, and overall business processes.
Here, AI algorithms are trained on massive data and real-world use cases to identify anomalies and report them in real time. Unlike other cybersecurity tools that address only one segment of a security environment, AI can support risk detection, prevention, response, and recovery. It adds speed and high scalability to the threat detection process.
Businesses worldwide are proactively integrating AI to strengthen their cybersecurity framework. Reports show that the global industry for AI in cybersecurity recorded a valuation of $30 billion in 2024, which is expected to surpass $134 billion by 2030.
Benefits of Using AI for Threat Detection:
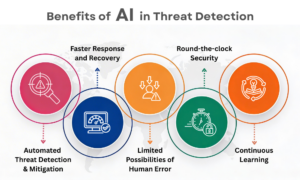
Integrating AI systems for cyber threat detection can bring several other benefits. While enabling real-time threat intelligence, AI models also continuously evolve through consistent learning. Let us discuss the most significant benefits that businesses can utilize in this regard-
Automated threat detection and mitigation: AI processes automate the threat detection and prevention methods. It consumes limited time, saves efforts, and sustains a robust security framework.
Faster response and recovery: While manual threat detection consumes significant time, recovery becomes lengthy and challenging. AI-driven tactics address this gap, offering faster response and recovery.
Limited possibilities of human error: Human error has been a significant hurdle in cybersecurity. While AI strategies require little human intervention, the possibilities of human errors are reduced.
Round-the-clock security: AI-driven threat detection offers 24/7 monitoring and security. Security threats can take place anytime, even if systems are idle. Under such situations, AI-enabled strategies can detect threats and issue alerts at the earliest.
Continuous learning: AI algorithms continuously evolve while integrated in cybersecurity. They analyze the real-world use cases of incidents consistently to detect new threat patterns and send alerts.
Which AI Capabilities Are Beneficial for Threat Detection?
- Supervised Machine Learning: This AI technology uses labeled datasets to help identify known threats and categorize incidents.
- Unsupervised Machine Learning: It goes beyond labeled datasets to identify unknown or zero-day threats.
- Reinforcement Learning: It acknowledges feedback loops and adopts trial/error to learn optimal defensive steps.
- Deep Learning: DL uses neural networks to analyze traffic and logs. It helps in finding complex patterns in datasets.
- Natural Language Processing: NLP undertakes unstructured text and language analysis to detect anomalies. For this purpose, it can assess emails, conversations, and logs.
- Large Language Models (LLMs): LLMs analyze unstructured data to gather details on threats and simulate them to identify possible threat attempts.
Use Cases of AI-Driven Threat Detection:
Real-time Anomaly Detection:
AI-enabled processes analyze and understand the standard baseline of the usual network, users, logs, and organizational functionalities. Hence, it can easily identify unusual patterns in login attempts, data access, and sudden surges in traffic.
Whether it is an external threat attempt or an internal error, AI-driven strategies identify anomalies in real time and issue alerts. Organizations can accordingly take steps to further assess the compromise and address the same.
Insider Threat Detection:
AI can operate round-the-clock and monitor user activities within an organization across systems, tools, and software. It can track suspicious activities and patterns when an insider tries to abuse privilege, access data without permission, steal data, or vandalize systems.
The AI-driven framework generates alerts once it identifies attempts to compromise security firewalls and unauthorized data access.
Network Intrusion Detection:
Network intrusion indicates unusual activities across a network, such as unauthorized attempts to access data and connected devices while compromising confidentiality and integrity. AI systems track these abnormal activities, even the minor ones, at the endpoints to detect threats and send alerts.
Malware and Ransomware Detection:
Manual detection of malware often fails to identify polymorphic or continuously changing malware strains. In this regard, AI capabilities analyze unknown system interactions, execution activities, and file or software characteristics autonomously to detect threats. It is a behavioral analysis that sends alerts for probable malware and ransomware attempts that have limited identifiable strains.
Unignorable Limitations of Integrating AI for Threat Detection:
Inefficiency Led by Low-quality Data: AI models for cybersecurity are tuned with vast amounts of real-world data. If they are trained on incomplete or poor-quality data, there is a possibility of missing threat attempts or false alerts. This can create unnecessary disruptions across an organization.
Data Privacy and Security: While operating, AI systems collect and analyze organizational data, including endpoint details, confidential logs, network traffic, user details, and other information. At times, AI can collect more data than required. While AI models are also vulnerable to attacks and breaches, the sensitive data of organizations is also at risk.
AI-Driven Attacks: Cyber criminals also target AI models to execute poisoning, adversarial, and evasion attacks. Such attacks can lead to stolen data, credentials, and misuse of the same. This is an alarming risk of AI-driven threat detection, indicating that cybercriminals can also exploit the key player, that is, AI, in a security framework.
Integration and Expertise: The implementation of AI tools for threat detection requires expertise and specific skillsets. Even after deployment, these tools need continuous surveillance for better and more effective performance. This can be a challenge for organizations since they need to build a dedicated team with the right talent to manage AI systems for security purposes.
Adopt AI Responsibly for Threat Detection!
Cybercriminals are continually evolving, developing advanced methods to execute attacks. To address such critical situations, adopting proactive security solutions is nothing but a necessity for organizations across the globe. Automated threat detection, real-time analysis, and immediate alerts are what we need to mitigate sophisticated cyber-attacks.
AI-enabled capabilities can surely strengthen firms' security approaches, while offering real-time threat intelligence and meeting all security needs. However, AI-driven threat intelligence also has specific limitations that organizations need to consider while integrating such strategies.
Hope our blog has given you a clearer idea of how AI-enabled strategies can help address modern cyber threats in real time, along with their major limitations. Read our other informative blogs to understand the cybersecurity practices thoroughly.
FAQs:
Q1. What are the four types of threat detection?
Answer: Signature-based, anomaly-based, behavior-based, and threat intelligence-based are the four types of threat detection.
Q2. What are the 5 stages of threat intelligence?
Answer: Planning and direction, collection, processing, analysis, and dissemination are the 5 stages of threat intelligence.
Recommended reading:
What is Automated Threat Detection and Response?
Threat Detection and Response (TDR) in Cybersecurity: Explained
XDR and AI: A Powerful Combination for Advanced Threat Detection
The Rise of the AI-First SOC and Its Revolutionary Impact on Cybersecurity Threat Detection